What is the Best Access Control Management Software
Door access management software is an essential part of your access control system. It allows you to manage the door readers in your organization, enter credentials for each person, and manage all the people who will use the doors.
Most of the access management software available provides simple door reader management. You can control who, when, and where people can enter. What else do you need? It depends on your requirements.
Additional features will allow you to determine who is in the building, manage the system using your mobile device, lockdown the building in an emergency, and many other features. Here is a review of some of the things you may want to consider when you select your door access control system.

The more powerful products provide a wide variety of capabilities that cover many different situations. This article reviews some of the key features and functions that you may need for your access control system.
Access Control Management Determines Who Can Enter
Who can enter a door is established when a credential is assigned to a person and entered into the management system. The credential number is entered manually or by swiping the card. The person’s name, their privilege level, maybe their picture, and other information is entered at this time.
Access Privilege Defines Who, When, and Where a Person Can Enter
Each individual can be assigned to specific groups. For example, office workers can enter the front door only from 9 am to 5 pm. The management team can enter through the front or back door, and can enter anytime between 8 am and 10 pm. The security person can open any door at any time. All this is controlled by setting up access privilege groups and then assigning the people to each of the groups.
Biometric Door Readers
A biometric door reader assures that the right person enters rather than the right credential. With a biometric reader, you don’t need two-factor authentication, or pass-back control, because it authenticates the person. Biometric readers can read your fingerprint, your face, or the veins in your finger to verify who you are.
When Can a Person Enter Increases Security

Access management software allows you to control when people can enter. The time and day are controlled by a calendar function.
When a person is entered into the access control system, you can assign them to a group, and then schedule the group for the appropriate days, times, and holidays that you would like.
Enter Holidays and Special Events
Advanced systems not only allow you to enter holidays, but they also allow you to establish special events. In this way, your organization can schedule an open-house and adjust who can come for that one particular event.
Establish Time Zones
What happens if your organization is spread over multiple time zones? You could have each area control their own doors, but what if you want to have a centralized management center? The ability to create time zones makes access control setup and management much easier.
Special Times for Certain People
Access management systems can also control when people enter a specific area. For example, it may be helpful to allow certain people to enter the exercise room at certain times of day, while others are allowed to use the room at a different time. There can even be special holidays assigned to different floors of a building.
Where a Person Can Enter and Leave
Access control management software determines what door a person can use. Each door can have its own list of rules. You can define who can enter and when they can enter. By assigning a person to a specific group, you can control everything they can do.
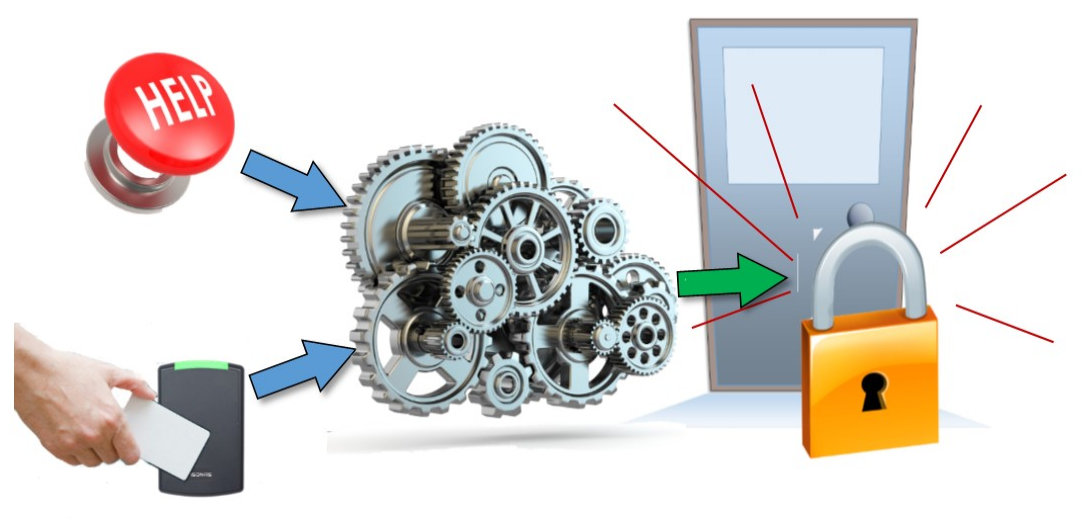
Handling Special Situations
In a crisis, it may be necessary to change how the door locks behave. In an emergency, you can prevent certain users from opening a door. This can be done using the administrator console, or a panic button. You can establish each users security level and then assign these levels to the crisis groups. In a crisis, anyone with a higher security level can use the door while the lower levels can’t open the door.

Emergency Situations
In an emergency, you may not have time to use the administrator console. The crisis mode can be initiated by using a button. The button is connected to one of the controllers and provides the trigger that initiates an emergency status. For example, a button can be pressed to create a lockdown or fire alert. Another push-button can be used to return the system to regular operation, or you can use the administrator console.
Note that this type of function is usually associated with “If-Then” logic and is not available in all access control software management systems. See the description of If-Then logic below. If the software doesn’t include this function, it would be necessary to run wires to each IP door reader/controller.
Management Functions of Door Access Control Software
The best door access control management software should be easy to use. The software should have an excellent user interface that provides clear prompts that most people can understand. The management software is associated with the specific door access IP door readers and controllers. There are access control management software for the Isonas systems, the Hartmann access control system and the biometric IP door access systems.
Multiple Site Control
The advanced door access management systems are designed to be used in large multi-location organizations. Partitions can be established with different management control so that a person can be assigned to manage their own location while central management can manage and control all the locations. For example, a school board may have many schools. The superintendent of the district can log in to the software and see all the schools, but the principal at each school can only log in and view and manage their individual building.
Reports
The access control management software provides reports that allow you to track the activities relating to door access. The report can show the time someone entered and the door they used. If you add door readers for exit control, you can tell when the person left. Only authorized system administrators have access to these reports.
The reports can also tell you when access was denied. You can tell if an ex-employee tried to use their credential to get in, or if a credential was used in an anti-passback violation. By using an optional IP camera system, you can match the people with the credentials used to open a door.
Advanced Features of Access Control Management
There are a variety of things that can be provided to make it harder for the wrong people to gain access to your facility. Features such as access privilege groups, two-factor authentication, anti-pass-back control, mantraps, biometric door readers, and integration with IP camera systems provide extra levels of security.
Two Factor Entry Authentication
Security can be increased by adding two-factor authentication. If someone gets hold of someone else’s credential, the addition of a security pin number will reduce the chance that they can enter using a stolen card credential. The dual entry authentication requires a reader with a keypad.
Anti-Pass-back Control
We can’t guarantee that the users of an access control system will always follow the rules. Sometimes they bring a visitor that will use the same credential to enter the facility. Ant-pass-back control reduces this situation by allowing a credential to be used only once within a certain period of time. Now when another person tries to use it at the same door or even another door, the system will prevent entry.
Mantrap Access Control
Some organizations require a very high level of security. A mantrap is a small room with two doors. It’s like an airlock. The doors are interlocked so that a person entering the first door must wait for the door to close before opening the second door. This can be automated, or it can be controlled by a guard. An intercom and an IP camera are placed in the small room so that the security guard can monitor and control entry. The mantrap function is provided by hardware and software. The configuration requires two readers, one for the outer door and another for an inner door. A two-way mantrap requires four readers.
Two-User Authentication
Some systems provide the capability to add two people (or two credentials) to open the door. In this case, two people need to swipe their cards (credentials) to open the door. They must swipe their cards within a preset time period.
Real-time Door Access Monitoring
If you have a security department that is actively monitoring your organization, the access control management software can provide immediate alerts. For example, if an old employee tries to use their credential to enter, or if the anti-passback control is violated, the security personnel will be notified.
If then Logic
Some access control management software systems include “if-then” rules. This logic control establishes a set of rules that allow you to react to specific inputs and then define output consequences. It is a powerful feature that adds flexibility to a door access management system. Some of the systems provide some form of if-then logic. For example, if a button is pushed (connected through a reader or controller), the system could lock all the doors. Another example is to use a special card to unlock all the doors.
In some systems, a credential can be triple swiped to cause an output action to occur. The logic is used to implement many different types of actions such as locking all the doors, enabling an Aux output from one of the controllers that trigger an audible alarm, or to disengage a security alarm system.
Elevator Control
Some access control systems include elevator control. This allows you to restrict access to specific floors for certain people. An elevator control system includes specialized hardware as well as the management software. The access control management software allows you to manage all your doors and the elevators using the same management system.
IP Camera System Integration
Integration with IP camera systems improves the security of the facility. It allows you to see who has entered the door. This allows you to check if the right person used the credential to open the door.
The simplest solution is to use an IP camera system with its own video management software (VMS). This requires two applications to be available on the computer you are using. By entering the time-date stamp from the access control system, you can locate the associated video for a nearby camera. A better approach is to use door access management software that integrates with the VMS. Some access control management software will show a snapshot of the person entering the door while others will include a video stream of the event. Integrated systems can provide multiple camera views at the same time so you can not only see who has entered a door but also other areas near the door.
Access Control Management Software Summary
The access control management software is an essential part of the modern door access control system. It provides the tools for entering all the users and establishing when and where they can use specific doors. The advanced management software makes it easy to control many sites and provides additional features that increase safety and security.
Please contact us for help selecting the right access control system. We can be reached at 800-431-1658 in the USA, or at 914-944-3425 everywhere else, or use our contact form.