Access Control Systems
Learn More About Door Access Control | Purchase Your Access Control System

Kintronics is an Engineering-Focused Solutions Provider
We offer complete IP door access control systems at competitive prices, along with free expert consultation. Because every environment is different, the access control system that works well for one application may not be the best choice for another. Our team helps you evaluate your specific requirements and select the right solution for your facility.
We believe informed buyers become the best long-term customers. That’s why Kintronics puts education first, helping you clearly understand your options, technologies, and trade-offs before you invest in an access control system. We provide resources and a comparison chart that help you choose the best access control system.
Quick Links:
Select the Type of System
What kind of Door Access System is best
Review the Buyers Guide
Comparison of Access Control Systems
Select the Software
What is the Best Access Control Management Software
Select the Door Reader
What is the Best Door Reader
See the Video
How to Learn More

Q & A
Questions About Access Control
To learn more:
- Select the Type of Access Control System: Choose a simple, full featured or a biometric system.
- Check our Buyers Guide for help selecting the right access control system. You can also learn about The Real Cost of Access Control, and How to Justify the Cost of Access Control Systems. You can also view our video, Door Access Control Purchase Guide.
- Access Control Software: What is the best management software for your requirements.
- Access Control Door Reader: Select a simple card reader, smartphone, or Biometric Reader.
- See the video How to Select the Best Components for your access control system.
- Do you need more information? Check the Access Control Q & A or Contact us.
We provide Free Consulting so that you get exactly what you expect
Door Access Control Resources
Why are resources important? The resources help you set your objectives and determine what is best for your organization. We provide all the information you need before you make a purchase. For example, see How to Select the Best Door Reader. Other resource articles cover How it Works, What to Consider Before Buying, How to Choose the Best Access Control System, a Comparison of the Latest Door Readers, and more.
We believe that an educated market is our best customer. The resources on this site enable you to know what you are buying and how it meets your requirements.
Comparison of IP Door Access Control Systems
There are many types of door access control solutions available, each designed to meet different operational requirements. For smaller organizations, an access control system that uses a door reader with a built-in controller can provide a simple, reliable, and cost-effective approach to access management. Larger facilities may require an enterprise-class platform, such as the Hartmann Controls enterprise solution, which supports large deployments and advanced features like elevator control and integration with IP camera systems. For environments that demand the highest level of security, biometric access control systems are also available, using credentials such as facial recognition, fingerprints, or palm verification.
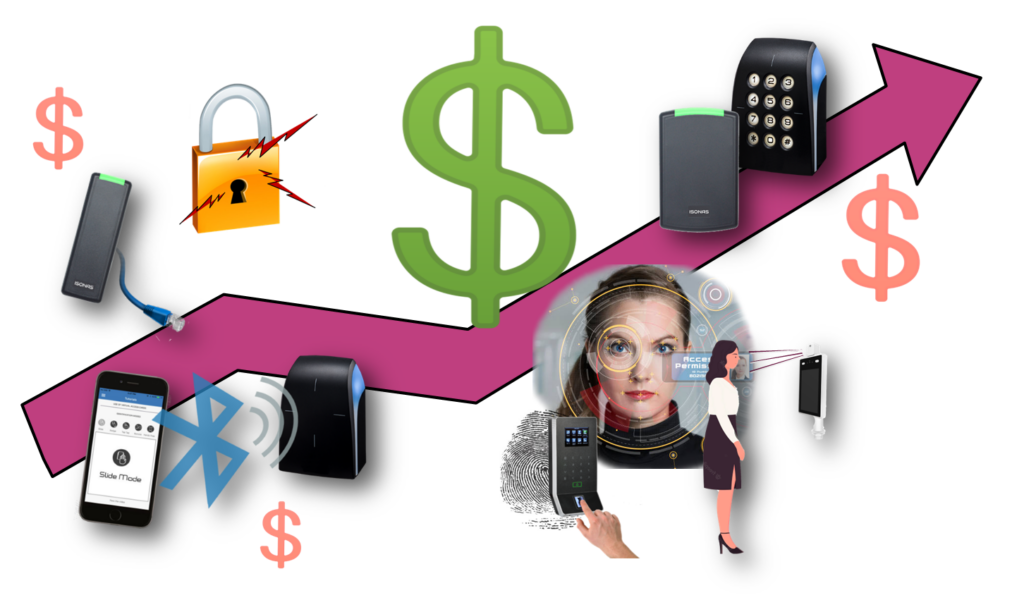
Your choices also extend to the door readers themselves. Credentials range from traditional card readers to mobile-enabled readers and advanced biometric devices, allowing you to balance convenience, security, and budget.
When integration with other systems, including IP cameras, intercoms, or paging, is required, more advanced access control management software can unify these technologies into a single platform.
How to Purchase Your Access Control System
Why Purchase from Kintronics? We believe informed buyers make the best long-term customers. That’s why Kintronics focuses on education first, helping you understand your options before you decide to purchase.
When you clearly understand what you’re purchasing, you can confidently choose an access control solution that fits both your operational needs and your budget.
- Call us at 914-944-3425. We are available 9 am to 5 pm EST, Monday through Friday, except holidays. If we are not there, leave a message and we will call you back.
- Or, fill out our request form, or send us an Email dennis@kintronics.com
- When you send a message or call us, real people answer your request. They will make sure that you receive exactly what you need.
- Kintronics is your trusted source for door access control systems, offering competitive pricing and free expert technical support. Our experienced technical sales team works closely with you to understand your objectives, explain how each solution meets your requirements, and guide you toward the right system at the best value.
- You can also read the Access Control Overview or use the access control resource information.
Why don’t we have an on-line store? Because selecting the right solution isn’t a one-size-fits-all decision. We’ve found that our customers get better results by talking with us directly. That way, we can understand your specific requirements and recommend the right combination of door readers, credentials, electric locks, and access control software for your application.
Did you know that you can install one door reader at a time? The new IP Reader-Controllers connect to the network and are intelligent. One of the most significant advantages is the ability to install one door at a time. Please read our article, Scalable Door Access Control to learn more.
Do you have questions about door access control? You can look at our Q & A page or call us at 914-944-3425 or use our contact form.
Things to Consider Before Purchasing Your Access Control System
Several factors should be considered before selecting an access control system, including the system’s cost. Here are some key factors to consider before purchasing your system.
Access Control Considerations
The system controls who, where, and when a person can enter your facility. However, there are many other things that you should think about before purchasing the system.
Things to Consider include the type of door readers, where the controller is located, installation, the type of electric door lock, local compliance and regulations, the user management software, and more.
For a quick review of how to select your access control system, see our video, “Door Access Control Purchase Guide.”
What is the Real Cost of an Access Control System?
Like many other products, you can find inexpensive door control devices on Amazon, but it’s essential to know what you’re getting and whether it meets your requirements. If you search online, you might find a door access control kit for $80 to $125 per door. At first glance, that sounds like a bargain. But before clicking “Buy Now,” it’s essential to ask: Is that the real cost of an access control system?
You can also see our short video.
Access Control Purchase Guide
Door access control provides increased security, but there are other important things to consider when selecting your system. These objectives should encompass your current needs and anticipated future requirements.
A door access control system consists of door readers, controllers, management software, and other devices that can enhance your security, such as elevator and gate controllers.
The short video provides guidance on how to select your system so that you have no regrets in the future. You can also look at our Door Access Control Purchase Guide article.
When to Consider Upgrading Your Access Control System
Door access control systems are a foundational part of any physical security strategy. Yet many organizations continue to rely on systems designed for a different era, systems that lack today’s security capabilities, flexibility, and intelligence. If your access control solution feels rigid, outdated, or difficult to manage, it may be time to consider an upgrade.
You can watch this video or read our article to help you decide when you should upgrade your Access Control System.
How to Select the Door Reader
The door reader is a critical part of the access control system. You should consider your objectives for each entry point. Things to consider include the security level you need at the door, the type of credential you would like, the management and maintenance cost, and ease of use.
This video provides guidance for selecting the best door readers for your access control system.
You can also read our article, How to Select the Best Door Reader
“The most exciting phrase to hear in science, the one that heralds new discoveries,
is not ‘Eureka!’ but ‘That’s funny…’”
Isaac Asimov
What is Door Access Control
The more you understand about access control systems, the easier it is to select the right solution for your facility. When you understand how these systems work, you can make better decisions about security, scalability, and long-term performance.
Why Understanding Access Control Is Essential
An Access Control System is a collection of devices that manage and control physical access to a building, room, or restricted area. Its purpose is simple but critical: allow authorized individuals to enter while preventing unauthorized access.
Door Readers | Door Controllers | Management Software | Locks | Purchase | Learn More
How an IP Access Control System Works
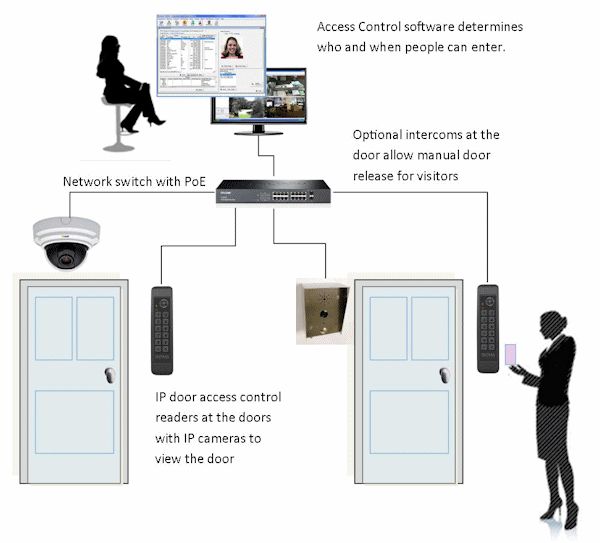
Modern IP Access Control Systems connect directly to your network, providing greater flexibility and easier integration with other security technologies.
The Access Control System includes Door Readers that detect the unique identification number (ID) provided by the credential. The Credential can be an RFID card or keyFob, a person’s smartphone, or their biometric (for example, their face or fingerprint). An access control system also includes a Door Controller and Access Control Management Software that manage all aspects of the system. It determines who can enter, when, and what door they can use. When a registered credential is detected, the controller releases the Electric Lock. Access control systems can be used to monitor who enters and exits a secure area, generate reports, and provide data for security analytics.
An IP Access Control System differs from the classic analog systems in that it connects to the network. IP door access control provides increased flexibility, easier installation, and easier integration with other IP security systems such as IP Camera Systems.
Access Control Systems provide increased safety in today’s heightened concern for security. Kintronics provides everything you need to create an advanced door access security system.
The Purpose of Door Access Control
The IP Access Control System is used to prevent unauthorized entry. Credentials, like a card or keyFOB, a mobile credential, or a biometric credential are used to identify the person who can enter the door. The access control system determines who, where, and when a person can enter the premises. The IP access control uses the IP network for communication to the management software and allows remote management over network attached devices such as smartphones. .
Access control is crucial for safeguarding assets, information, and people while providing operational benefits. It helps maintain order, privacy, and efficiency in various environments, contributing to a safer and more secure facility.
Door access control system can tell you who is in the building. It can also notify security the moment a vehicle enters the parking lot? Take a look at the article Security Questions and Answers.
Did you know that intercoms play an important role in Door Access Control. They ensure that guests can enter the facility. To learn more read our article, Access Control and Intercoms: The Perfect Match.
Door access is only one part of an integrated security system. For example, by integrating door access control with IP camera systems, we can create a holistic security system. You can also integrate IP intercoms that control visitor entry. This strategy integrates all the elements designed to safeguard an organization into a multifaceted and interconnected Physical Security System. The endgame of this holistic approach is to provide a continuous level of protection across the organization’s community, and the physical environment.
Did you know that biometric door readers such as face and palm recognition are the most secure access control devices. Read more…
An access Control System offers financial benefits. For example, they help organizations reduce costs, improve efficiency, and protect assets. Please read our article “The Financial Benefits of Access Control” to learn more.
Your safety is built around four primary types of security equipment: door access control, IP intercoms, IP cameras, and emergency paging systems. Door Access Control is your first line of defense.
Take a look at our article Access Control Comparison Chart to learn more.
Access Control is Part of a Physical Security System
Integrating door access control, IP camera systems, intercoms, and IP paging is one of the best ways to create a comprehensive and highly secure physical security system. When these components work together, they provide real-time surveillance, controlled access, seamless communication, and rapid emergency response. To learn more, read our article How to Maximize Physical Security.
Access Control and Visitor Management work together in provide security
This video shows how Access Control and Visitor Management work together:
Components of the Access Control System
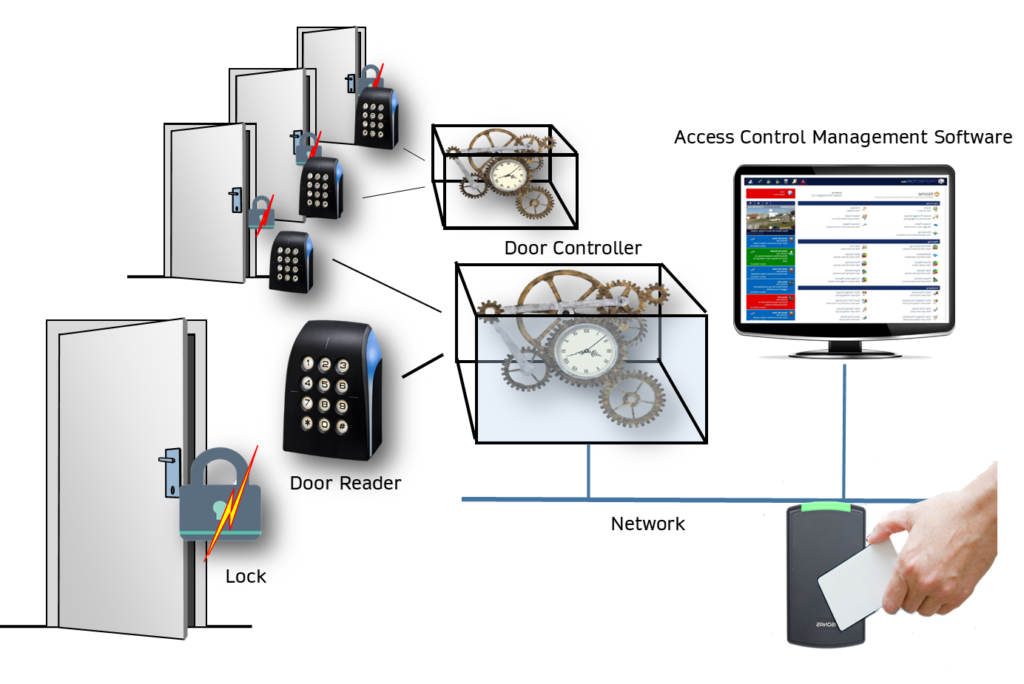
The door access control system includes:
- The door reader reads the credentials and connects to the access controller. Learn more…
- The Access Controller Box contains the door management part of the system. It controls the locks on the doors, connects to all the door readers, and attaches to the network. The controller also interfaces with the access control management software. Some systems use a separate controller; others have the controller built into the door reader. Learn more…
- There are three families of controllers. The Pro controller is used with RFID readers, while the Pro-bio controller adds support for a fingerprint reader. The Enterprise controller is used with many types of door readers, including those supporting mobile credentials.
- Select a Controller: Enterprise Controller | Pro Controller | Pro-Bio Controller
- The Intelligent reader-controller combines the functions of the reader and controller in one box and attach to the network.* Learn more…
- The Access Control Management Software maintains the list of people who use the system and manage the access control system. Learn more…
- Credentials identify a person that can enter the doors. A credential can be something you carry like a card, your mobile phone, or a biometric credential such as your fingerprint or face. Learn more…
- The Electric Door Locks are controlled by the access controller. It’s important to consider local regulations when installing mag-locks. See our article Access Control and Fire Alarm System Integration to learn more.
- Intercoms control visitors and enhance security. They ensure that guests can enter the facility. Learn more…
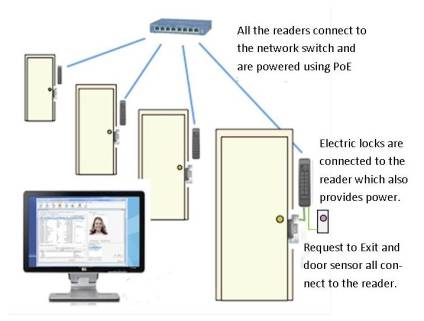
*The IP reader-controllers are significantly different than the older door access systems that used central control boxes. Instead of connecting to a control box, they connect to your network and are powered by PoE.
If you want to learn more about how the access control system works, how to install it, or what is the best door reader, take a look at our resource articles.
Product Highlights
Door Access Control Purchase Guide
The Regret Free Guide to Access Control
You have been asked to select an Access Control System for your organization. The “ask” could have been from your boss or maybe from people around you who requested more security. Besides increased security, what are your key objectives when selecting the right system?
This article provides the information you should consider before purchasing your door access control system so that you don’t have any regrets later.
Door Readers for IP Access Control Systems
Door readers are devices at the door that determine your permission to enter. The first electronic readers were developed in the 1960s. They had a keypad allowing users to enter their credentials. This PIN (Personal Identification Number) permits entry if you enter the correct number. Over the years, many types of door readers have been developed that are safer, simpler to install, and easier to use.
This article reviews some of the most popular door readers and provides each type’s advantages and disadvantages:
Door Access Control Justification
Door access control systems have become much more valuable these days. They have always provided significant security benefits and have evolved to provide many more advantages. The most important technical advance is the use of IP-type access control devices.
Implementing an access control system is a strategic move to enhance security, streamline operations, and ensure organizational compliance. This article describes how you can justify the investment in door access control. Read more…
The Best Long-Range Access Control System
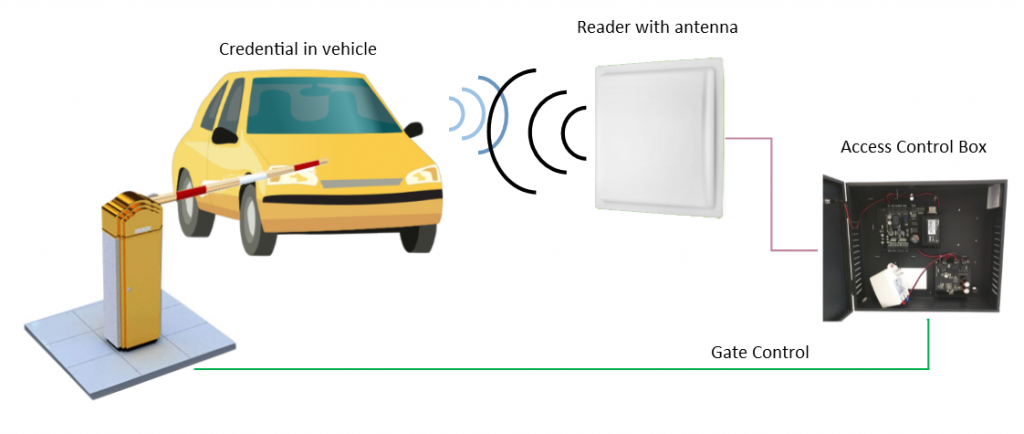
When to use long-range access control systems: Standard door readers have short-range capabilities that read your credentials, but if you want to access a garage or open a gate, the reader requires a more extended range.
Long-range access control systems are usually used to control gates and garage doors. They extend the capability of door access control systems. They read a credential to open the lock. The standard access control systems have a card-to-reader range in inches, while the long-range readers have a range of over 25 ft. When you want to open a gate to a parking garage from your vehicle, it’s easier to use the long-range reader system.
Long-range access control reader systems use large antennas and credentials with a battery. The larger antenna allows more energy to be directed at the credential. Systems that use passive credentials (no battery required) have a maximum range of a couple of feet. The active credentials with batteries have a more extended range, but the battery needs to be replaced. Learn more …
Additional Security Solutions
Here are some additional products that increase your safety and security:
Temperature Scanning and Mask Detection at the Door
Special access reader-controllers include palm recognition, face recognition, and scan for elevated temperature as well as checking if you are wearing a protective mask. Read more…
Contact Tracing for Disease Prevention
When a person is diagnosed with Covid-19 or another communicable disease, finding all the people they have had contact with is important in keeping your organization healthy. This contact detection system reduces the spread of disease. Read more…
Did you know that Apartment Intercoms provide an excellent way of increasing safety. They can even control the floor a visitor can go to. Read more…
IP Door Access Control for Small to Enterprise Systems
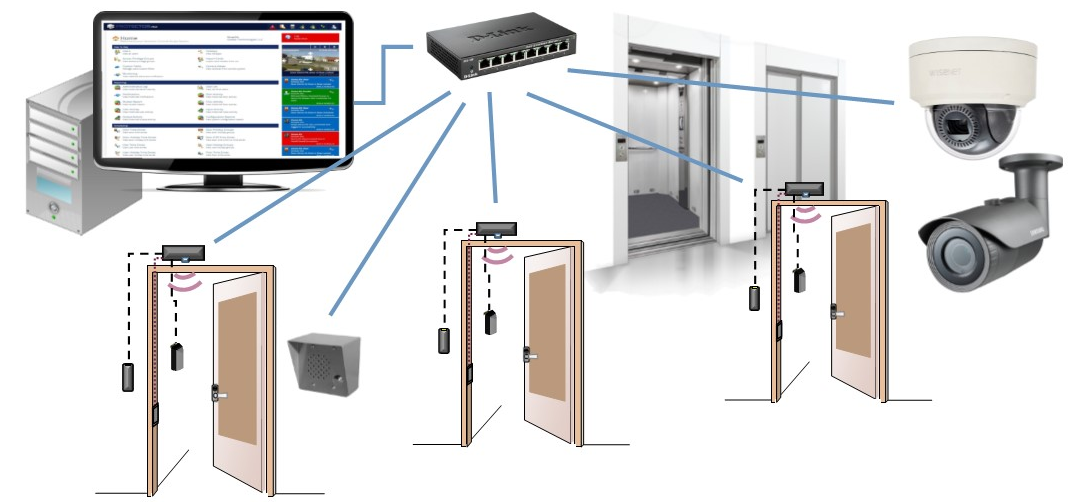
Why select the enterprise-type access control system: The enterprise access control system provides advanced functionality designed for complex access control environments. The Hartmann Controls advanced access control system enables you to start with a single door and scale up to thousands of doors and users. Since each door includes its network-attached controller, it is very easy to expand the system.
The Hartmann IP door access control system features powerful access control management software, supporting elevator control, if-then logic for advanced functionality, and integration with IP camera systems. The access control management software offers on-site and mobile control, providing management wherever and whenever you need it.
For more details take a look at the access control system diagram.
Door Access Control Features:
- The door access controller uses Power over Ethernet (PoE)
- A very flexible controller that can mount on top of the door and provide a built-in motion detection function.
- Operates even if the network is down (as long as the controller has power).
- Supports multi-credential door readers including those that support mobile credentials.
- The same controller modules can be ganged together inside a central control box that can be used to retrofit older door access control systems.
- The controller provides connections with power for the electric lock, connections to exit buttons, door sensors, automatic door openers, and the electric lock control.
- There is an optional built-in motion detector that can provide the Request to Exit (REX) function.
- The controller can control two readers (inside and outside the door) or two separate doors.
- Integrates with many fire alarm systems
- 256-Bit AES Encryption: Protects data at a level often required by high-security environments such as financial, military, municipal and hi-tech organizations
- Includes integration with Video Surveillance Systems, elevator control, and fire alarm systems
Access Control Door Readers
The slave door readers connect to an intelligent controller such as the Hartmann controller. The readers support Radio Frequency ID (RFID) credentials that the person carries or mobile credentials provided by the person’s smartphone.
There are RFID credentials that use 125KHz or 13.56MHz, Mifare, or Smartcard format. The mobile credentials use Bluetooth connections to your smartphone. The Biometric Readers read a person’s characteristic like your fingerprint or face.
The Enterprise IP Based Door Access and Entry Control Systems Integrates with IP Camera Surveillance Systems
IP Door Access Control systems can be easily integrated with your IP camera system. We can maximize your safety and security in hospitals, schools, government, military, and other organizations. Now it’s easier than ever to install a door access control system using your existing Ethernet network. It can be easily integrated with an IP video surveillance security system.
To learn more see our article How to Use IP Cameras With Access Control.
As an example, the Hartmann enterprise door access system integrates directly with many IP camera video management software systems.
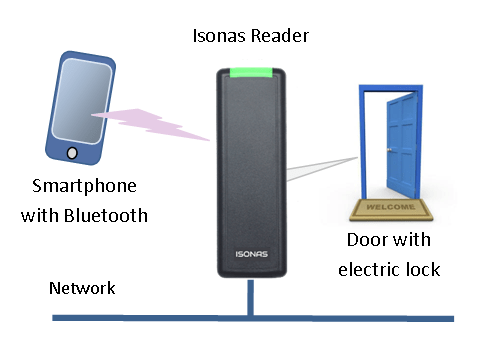
IP Access Control System for Small to Medium Systems from Isonas
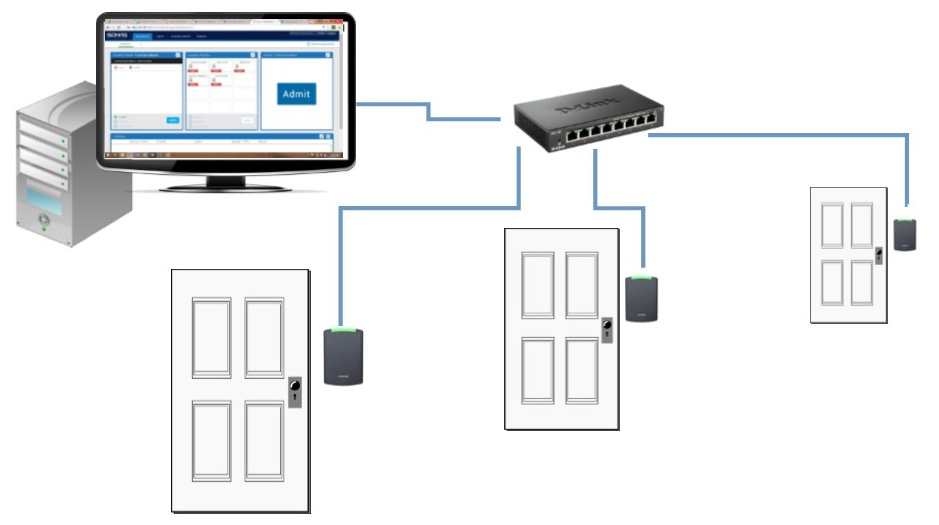
This modular IP based door control system allows you to add one door at a time. The expensive control panel is no longer required! The ISONAS IP Door Access Controller and Reader includes all the functionality that used to be in the control panel. Now it’s all in one unit. With intelligence built into each and every unit, it operates even if your network is down.
Each Isonas IP reader attaches directly to the network and is powered using PoE.
Features of Isonas IP Access Control System
- No Control Panels Required
- IP Door Readers are powered using PoE
- The readers provide 12 VDC power for the electric lock
- A wide selection of credentials and cards
- Pure Access Cloud or Pure Access Manager Software Required
- Works with IP intercoms to allow remote control of doors to allow entry of visitors
Isonas IP Door Readers for Access Control
ISONAS IP door readers are both an RFID Proximity reader and a controller. No control box is required since all the intelligence is in the IP reader.
Specifications for the Isonas Readers
The IP reader connects directly to the Ethernet network and is powered by PoE. IP door readers have the advantage of being very easy to install.
Since the reader converts the PoE power to 12 VDC, you can power locks without running additional power wires. All you need is the CAT 5 drop to the reader. The latest RC04 readers are available in a number of different styles and capabilities. You can select models that mount on the side of the door frame (mullion) or on the wall. The latest models provide the option to use your smartphone (Bluetooth) as the credential.
The readers have all the intelligence built-in so even if the network is down the reader keeps working. Of course, it’s best to use a UPS on the network switch or the midspan that’s providing the PoE.
Learn more about the Isonas access control system.
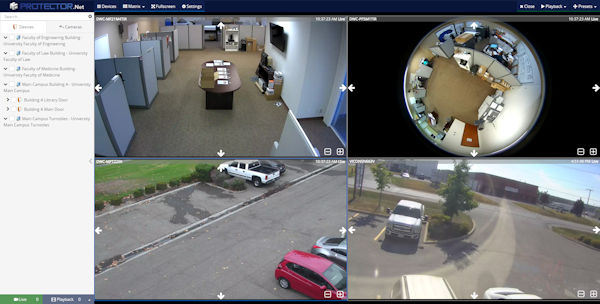
How to Integrate Access Control with IP Camera Systems
There are Access Control Management solutions that have the enhanced capability of viewing IP camera systems. IP Camera Systems provide surveillance of the organization. The combination of access control and IP surveillance systems offers a synergistic approach that significantly improves the organization’s safety.
Integration Solutions
Advanced Security Management Software
Advanced solutions provide Interoperable software that supports hardware from many different manufacturers.
They integrate with several IP camera Video Management Systems and support various access control hardware, making them an ideal choice for mixed hardware environments.
Enterprise Access Control System
The Enterprise door access control software manager integrates with many IP video recording systems. This includes many Video Management Software (VMS and Network Video Recorders (NVR)etwork
To learn more, read our articles How to Use IP Cameras With Access Control, and Comparison of Integrated Security Management Software.
More Details About Enterprise Access Control Systems
The Enterprise access control provides a very easy integration path with IP Camera Systems. Here is a short summary of how it is done.
The Enterprise door access control software manager integrates with many IP video recording systems. This includes many Video Management Software (VMS and Network Video Recorders (NVR).
- The video from multiple cameras is displayed in the same web browser as your door access management software.
- The real-time video can be displayed based on predefined alerts from the door access control system. The alerts include “Door Held Opened,” Door Forced Open, and many more.
- Examples of IP camera system systems currently supported include Hanwha Recording systems, Milestone xProtect, ViconNet, Exact, and Digital Watchdog systems. The list is growing so please check with us for the latest supported IP camera recording system support
- The software provides easy management of IP cameras
- You can create different viewing matrices so that you can view many different cameras at the same time.
- Easy playback of the recorded video allows you to select a time period and verify any security concerns.
- Cameras can be viewed on all platforms including desktop and mobile devices.
- Cameras can be associated with elevators, providing door/elevator alerts and history
Read more about Enterprise Access Control…
Integration with Isonas Access Control Systems
The Isonas IP-based access control system can be integrated with your IP camera surveillance system to provide a complete security system but requires additional integration software.
You can select the convergence database software that displays door entry information with the video captured when the door reader is used.
Biometric Door Access Control Systems Overview
Biometric Reader Overview | Select the Biometric Reader | Buyers Guide

The latest professional biometric readers provide increased reliability and functionality. Biometric door access control units attach to the network and measure a person’s unique physiological characteristics. Biometrics are the most secure type of credential. Note: They do not store a picture of the fingerprint or face. Everything is encoded for security and privacy.
Biometric IP door readers can be powered using PoE. Some of the readers use a splitter or 12 VDC.
Face Recognition Improves Safety
Face recognition is used to improve security, prevent crimes, and keep us healthy. The latest facial recognition systems use your IP camera system. They can be used for access control, and provide real-time information about who is entering specific areas in your facility, such as: recently terminated employees returning to work, restraining order alerts, a person of interest, people making threats to employees, contact tracing, etc.
Facial Recognition and Temperature Screening
Face recognition is used to check people’s temperature and track people within an organization. By maintaining a list of people who come in contact with each other the system builds a database that can be review for contact tracing.
Face Recognition and Access Control
Facial recognition is used for door access control. Door access uses face recognition algorithms that are built into the door reader.
Biometric access control provides a very secure way to control access to your organization.
Facial Recognition in a Crowd
Facial recognition can be challenging. Sometimes the person may not be facing in the right direction.
3D facial recognition extends the traditional methods of facial recognition to live-stream accurate capture and identification.
Biometric and Body Temperature Access Control
Designed for organizations that need more than door access control. These reader-controllers are access control systems that check a person’s temperature and if they are wearing a surgical face mask.
The face-recognition access control door readers combine a powerful embedded thermal camera and the latest face recognition algorithm that is supported by an optimized dual-core processor.
Summary of Access Control Solutions
- Simple and Easy to install and manage: Select the Isonas Door Access System
- Enterprise System with increased functionality and flexibility Select the Hartmann Door Access System
- When you require the highest level of security Select the Kintronics Biometric Door Systems
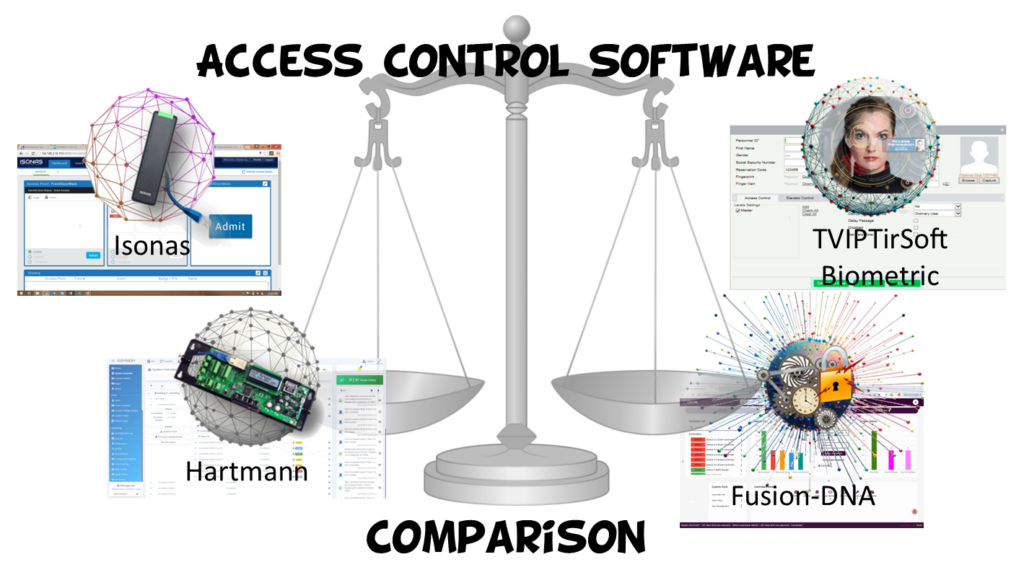
Access Control Management Software Comparison
Access control management software is a central component of modern security systems, allowing organizations to efficiently control and monitor access to their premises, resources, and information.
Access control management software determines who can enter, what door they can use, and when they can come in. Software is usually sold with a manufacturer’s hardware. The software controls the particular kind of door readers and controllers, so they must be selected with the matching system. Fusion-DNA is the exception to this rule. This interoperable software is designed to work with many different hardware products.
Comparison of Access Control Management Software
The following summary compares the various door access management software available:
Isonas Software
Pure Access is designed for the Isonas reader controllers. It is a Cloud and on-site software product.
- Provides basic access control functions
- Supports mobile credentials
- Includes a mobile app
- Supports 1 to 100 doors
- Doesn’t provide any advanced functions
Enterprise Software
This software is compatible with Hartmann Enterprise door access control hardware.
- Supports one to over 1,000 doors
- Includes elevator control
- Supports pass-back control
- Integrates with IP camera systems
- Includes if/then logic functions
Biometric Software
TVIPTirSoft supports Kintronics biometric door readers.
- Supports several types of biometric door readers
- Supports up to 2,000 door readers per server
- Optional software supports IP Cameras
Advanced Access Control Software
Advanced solutions provide Interoperable software that supports hardware from many different manufacturers.
- Works with a variety of hardware solutions
- Integrates with several IP camera Video Management Systems
- Includes customizable logic functions
- and more
Advanced Access Control Management Software
Advanced integrated Access Control Management software solutions
Provides easy integration with IP Camera Video Management Software (VMS), Elevator controls, and data management. It also offers excellent support with biometric door readers. It integrates with the WAVE VMS solution.
This solution integrates with numerous leading security systems to create a comprehensive security solution, encompassing video management, biometrics, audio communications, and more. It’s a complex system that supports a very large number of devices. Includes customizable logic functions and Visitor Management functions.
Acre purchased several companies in the physical security market. They offer a range of integrated solutions that support various physical security systems. The Acre solutions begin with an access control solution that supports up to 200 devices. It integrates with the WAVE VMS solution.
Benefits of Advanced Security Software Management
Advanced Security management software provides interoperability between several security management solutions. These software solutions are typically based on access control management or Video Management Systems, and then add additional components that enable easy integration with other security solutions.
To learn more about the different Access Management Software solutions available, read Comparison of Access Control Software.
Purchase
Isonas Access Control Software Solutions
The Isonas door management software is available as a cloud subscription. The cloud service, offered as a subscription, provides basic access control functions, making it a good small-to-medium solution. The downside is that it doesn’t support some advanced functions, such as elevator control.
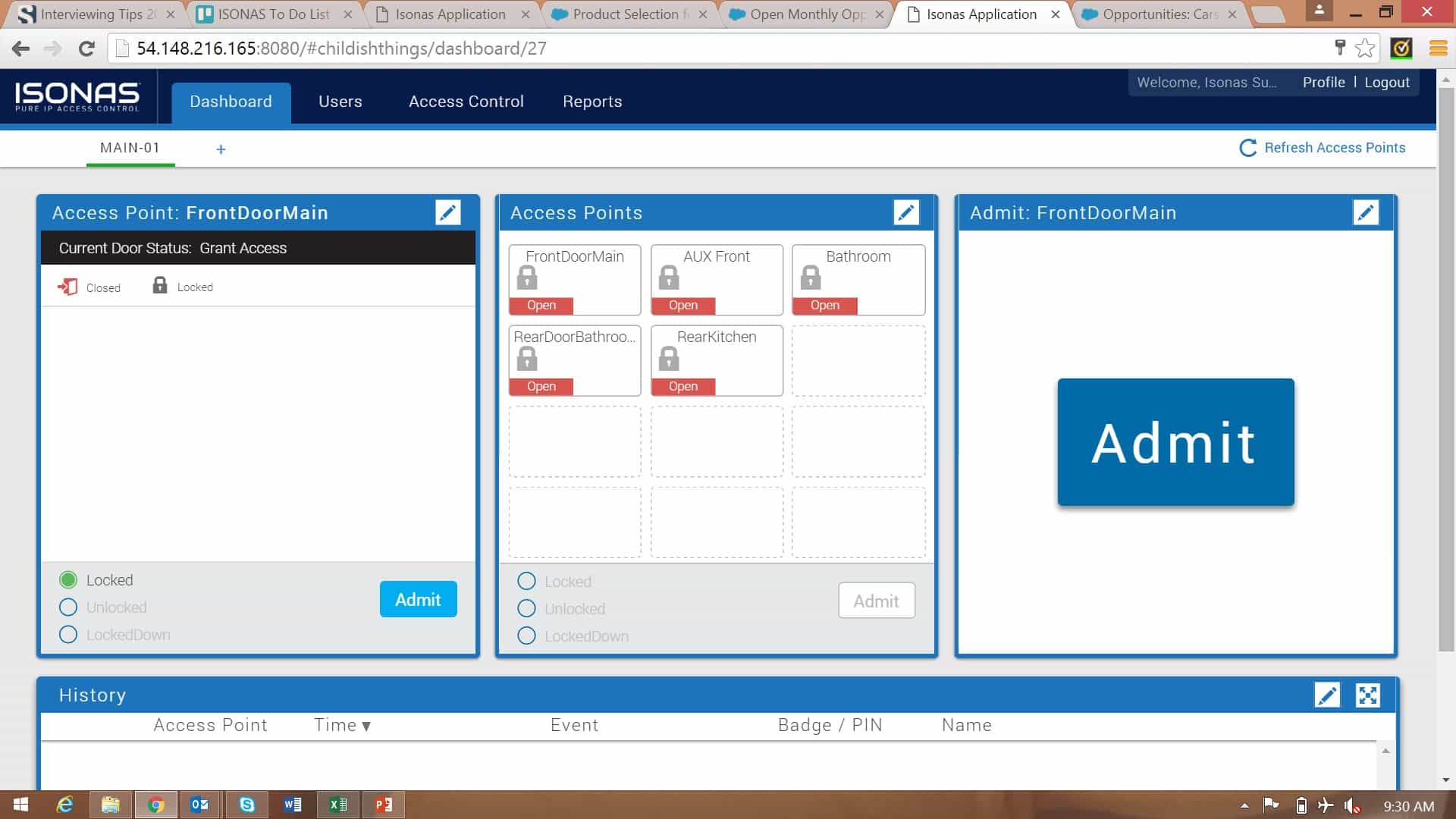
Pure Access Cloud Software
Uses a remote cloud server. Pure Access provides a complete hosted IP door access control platform available in the cloud. This allows full installation, administration, and management of your Isonas access control hardware. The cloud server makes installing and controlling your IP door access control system extremely easy. All the IP door readers and IP controllers can be installed from anywhere. Cloud software is provided under a monthly or yearly subscription plan.
Pure Access Manager Software (Discontinued)
Runs on your Windows computer. Pure Access Manager is on-premise software. This is the classic model of providing a perpetual license that allows you to run the software on your own Windows computer.
To learn more, please take a look at our article, Cloud Versus On-Site License, to help you determine which platform is best for you. Or, contact us for help selecting the right solution for your door access control application.
Legacy Software for Isonas Door Access System
DB Crystal Matrix Software™ has been discontinued and replaced by the Isonas Pure Access Manager. This software platform ran on your Windows PC and provided easy enrollment, allowing you to define who, where, and when people are allowed in. It used the SQL data structure making it very easy to integrate with video recording systems.
EasyWeb-2015 has also been discontinued and replaced by Pure Access. Contact us for details. Pure Access provides some enhancements that were not available in EasyWeb and provide similar functions to DB Crystal. The software is browser-based and enhances your access control system. It works with the latest readers. Pure Access Manager includes Active Directory integration to make it easier to register user rights. See the ISONAS end of life statement or contact us for more details.
See Cobalt software as an alternative to Easy-Web-2015.
Alternative access control software: 3rd party software is available that is similar to EasyWeb-2015. Cobalt provides many of the functions that were available before, including pass-back control and scripts.
Enterprise Access Control Management Software

The Hartmann access control management software provides advanced functions such as logic if-then functions, and allows you to control elevators, visitors, and integrates with IP camera systems. IP readers can also be used in parking lots to control a gate. These long-range access readers allow a credential to be over 25 ft. away from the reader. This access control management software is designed for the enterprise that requires advanced functions.
Features of Door Access Software
- Administer your Access Control System from any Browser-Enabled Device: Tablet, Smartphone, laptop or PC
- Easy Video integration into many video management software systems (VMS).
- Intuitive, easy to use action plan editor allows you to create complex action plans in minutes
- Flexible trigger engine allows you to trigger action plans from the door, input, output state changes, or trigger action plans upon scheduled times
- Elevator Control allows you to control what floor people can go to
- Active Directory support, on both the administrator levels as well as cardholder/user levels.
Biometric IP Reader Management Software Solution
This software manages biometric door readers. It is used for entering the biometric credential credentials as well as RFID credentials that can also be used with these door readers.
TVIPTirSoft
The Professional software supports all the Pro-series biometric IP readers and the Pro-series Proximity Readers. This management software is licensed per reader. There is no yearly subscription cost.
Proximity and Smart Card Door Credentials for Door Access
Select ISONAS, HID, Mifare, iClass format or Smart Card proximity credentials, or when you don’t want to use credentials select the Bluetooth Mobile Credential reader or biometric options.
You can select two different technologies, Prox-card or Smart-Card type. The Prox-card technology uses 125 kHz frequency between the credential and the reader, while Smart-cards use 13.56 MHz frequency. The smart cards provide additional levels of security. The credentials come in various form factors. Select the style you need: thin cards that fit in your wallet, clamshell-style that you can wear on a lanyard, Key Fobs for your keychain, or Cap Tags that can attach to other things.

Example of credentials available:
| RFID-type cards that use 125 kHz | Proxcard IIDuoProx II |
| Smart Cards that use 13.56 MHz and use AES128 encryption. | DESFire EV3 |
| Combination cards with both 125 kHz and 13.56 MHz capability | DuoProx |
| Different mechanical configurations | Clamshell, thin cardkeyfobs |
| Mobile Credentials | Bluetooth connection to your smartphone |
| Biometric credentials | Face, Fingerprint, Palmfinger-vein |
To learn more about credentials, please read our articles Comparison of Door Access Credentials and learn the pros and cons of different credentials, What are Door Access Control Credentials.
Note that pricing changes frequently so please contact us for the latest pricing. We can be reached at 800-431-1658 in the USA, or at 914-944-3425 everywhere else, or use our contact form.
Remote Door Access Control Using an Intercom and IP Camera
Intercoms for Apartments | Intercoms for Organizations
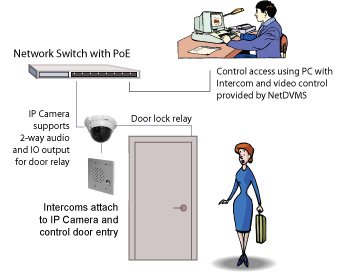
If you have a door that’s used by authorized people but can also have visitors, you can use our intercoms and IP camera systems to control the door. You can manually control entry from your computer.
For example, the intercom system notifies you with an audible alert, the video pops into a video window on your desktop so you can talk to the person at the door and then let them in.
There are a number of different intercom solutions depending on your exact requirements. Read more about intercoms
Intercoms for Apartments use wireless connections and smartphone apps to make it easy to control access in large organizations and apartment houses. Learn more …
Add IP Camera Systems to Door Access Control to Create a Complete Security System

Security can be improved when an IP camera system is added to door access control.
These combined systems maximize the safety and security in hospitals, schools, government, military, and other organizations.
Now it’s easier than ever to install IP camera and door access control systems using your existing Ethernet network. It can be easily integrated with an IP video surveillance security system. To learn more about integration of Door Access Control and IP Camera Systems read our article How to Use IP Cameras With Access Control.
Special Door Access System Solutions
Bluetooth Mobile Readers | Intercoms | Elevators | Long Range Readers | More
Door readers are available with special capability. The classic door readers use proximity credentials that use an RFID signal between the card credential and the door reader. Mobile credentials use Bluetooth connections to your smartphone. There are other special readers that provide longer range and can be used to open a gate from a vehicle. And, biometric door readers read your fingerprint or facial features to open the door.
There are other special door access systems that be used to control elevators. The access control systems can also be integrated with fire alarm systems, and for added security, you can add intercoms and IP cameras as well as walk through metal detectors.
Here’s a summary of some of these special access control systems.
These Bluetooth Readers Use Mobile Credentials in Your Smartphone
Mobile credentials are supported by the Isonas and some of the Hartmann door readers. All the Isonas IP readers allow you to use your Smartphone instead of a card credential.
The Hartmann Bluetooth enabled door readers support mobile credentials and have more flexibility than Isonas readers. They can unlock a door, open a gate, or even turn on lights with the wave of your hand.
Mobile credentials: Using your smartphone and an app, you can unlock your door.
Long Range Access Control
Special long-range door access readers are used to open a gate from your car. They have a range of over 25 ft.
Elevator Access Control
The elevator access control unit is used to determine the floors that can be reached based on the person’s credential. An elevator access control system consists of a credential reader in the cab and a controller box that is usually located in the elevator control room. Learn more…
Integration of Access Control and Fire Alarms
The door access control reader and the electric lock can be wired to the fire alarm in a number of different ways. We can use a relay to drop power to the electric lock, or use an IP device that drops power using the network connection, or add a power control box that drops power when the fire alarm system detects a fire. We can also use door access control software. Our article, “Access Control and Fire Alarm System Integration“, describes how this is accomplished.
Walk Through Metal Detectors
Adding metal detectors at the doors increase safety and security at your school, business or special events. These detectors assure that weapons don’t come into the building.
Visitor Management Systems

Visitor authentication and management systems enhance the safety and security of your organization. Today’s heightened interest in security and health has resulted in the need for visitor authentication. With the addition of access control panels and kiosks, you can provide temperature monitoring and protective mask detection.
These visitor management systems not only provide tracking of visitors they also provide visitor authentication and health monitoring. They can include access control panels that provide facial recognition, temperature monitoring, and mask detection to keep your organization safe.
To learn how Visitor Management and Access Control systems work together take a look at our video.
Access Control and Visitor Management systems provide an integrated security approach. They ensure that only authorized individuals, whether employees or visitors, can access facilities and sensitive areas. They monitor and log access for security and compliance purposes, and integrate with broader security measures for real-time response and investigation capabilities. This integrated approach significantly enhances an organization’s overall safety, protecting against both external threats and internal vulnerabilities.
Electric Locks for Door Access Control
Magnetic locks and Electric Strikes
Electric locks are a critical part of your door access control system. There are two common types of electric locks, electric strike and the magnetic (or Mag) lock. Each type has its place in the security provided by access control. Understanding the differences between these two types is essential to ensure the security and functionality of your access control system. To learn more about the right electric lock for your application, see the descriptions below and please read our article Access Control Electric Locks: Mags versus Strikes.
The following electric locks are available from Rutherford Controls (Dormakaba).
Magnetic locks are used in high-security areas where you need to monitor the movement of people. Since people are required to use their access cards in both directions, you can track who enters and leaves a secure area..
Electric strikes are easy to install and are used to secure outer and inner doors, but do not prevent egress from an area like the magnetic lock. It replaces the fixed strike place in a standard lock.
Special Cabinet Locks are available as well. For example, we have small locks that can be used to secure cabinets. These can be used to lock everything from filing cabinets to drug cabinets.
Resources for Door Access
More Technical Articles | Newsletter | Whitepapers | Blog | Videos
The following resources can be used to help you understand the technology. Contact us for help with your system. Our engineers will make sure you get the exact system you need.
Technical Articles
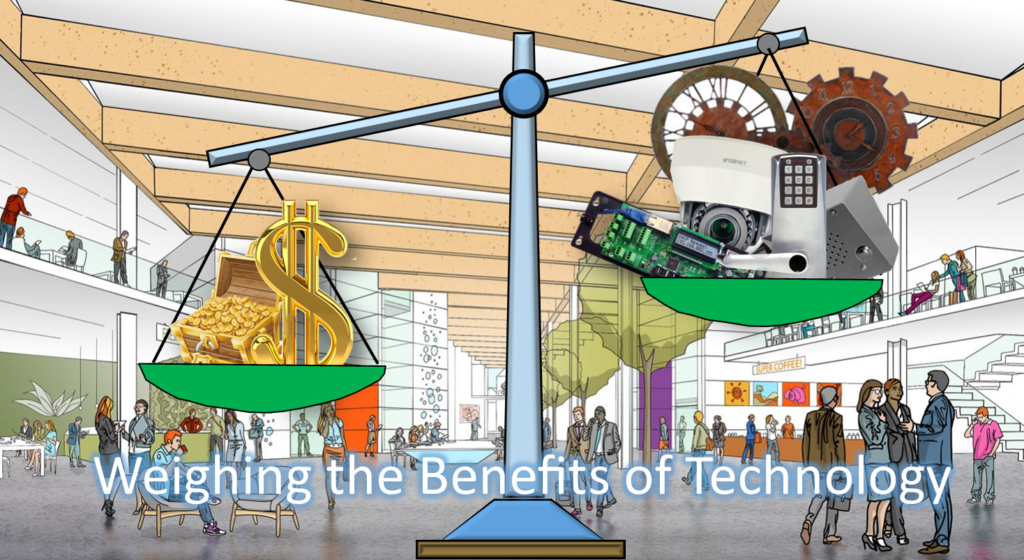
Weighing the Impact of Security Breaches
Security and safety are important issues in all organizations. Schools, hospitals, and businesses are affected not only by equipment loss and damage but also by possible injuries and stress caused by criminal intrusion. Physical security technology such as door access control, IP Camera Systems, Intercoms, and Paging Systems can prevent intrusions.
This article compares the cost of adding physical security to the impact of security breaches. Read more…
Comparison of Access Control Software
Are you planning to purchase a new access control system or upgrade an old one? The access control management software is critical because it provides many essential features and functions that will make a difference in the functionality of your access control system.
The management systems provide different features. For example, you may need elevator control, map functions, or integration of IP camera systems. This article helps you determine the best solution. Read more…
The Financial Benefits of Access Control
We all know that safety and security are significant advantages of adding door access control, but are there any financial benefits? It’s always best to analyze the return on investment of any new purchase. It turns out that access control systems offer several economic benefits to organizations, helping them reduce costs, improve efficiency, and protect assets. This article descusses some of the key financial benefits of access control. Read more…
What are Biometric Palm Readers
Touchless Palm Recognition uses a near-infrared (NIR) light source to illuminate the palm of the user’s hand. The hand is held near the sensor and doesn’t touch it. The blood in the veins absorbs the NIR light, but the surrounding tissue reflects it. This creates a unique pattern of light and dark areas that a sensor can capture. The sensor and computer then convert the image into a digital template stored in a database. Read more…
Access Control Installation
How to install Door Access Control: This article provides A Guide to Door Access Control Installation. Installing door access control requires mechanical lock installation, wiring, door reader mounting, and management software. You will find access control systems easy to install if you have installed other network-attached devices such as computers, IP cameras, or paging systems. Read more…
Biometric Door Reader Security
How to increase Access Control Security: Biometric readers are used instead of card readers to open a door. They identify a human characteristic, such as your face or fingerprint, and are much more secure than standard card credentials. Card credentials can be stolen, lost, or given to another person. This article compares some of the popular biometric readers. Read more…
Access Control and Intercoms
Intercoms provide control of visitors: This article from Kintronics explains how access control and intercoms can be used together to create a secure and reliable access control system. It explains how an intercom system can be used to verify the identity of an individual before allowing them access to a certain area. It also discusses the many benefits of using access control and intercoms together, such as providing a layer of security, as well as convenience and cost-effectiveness. The article also provides tips on how to get the most out of an access control and intercom system. Read more…
How Access Control Works
How Door Access Control Systems Work: Door access control is part of an overall security system that keeps our organizations safer. The access control system ensures that only registered people can enter the organization.
Door Readers for Everyone
Comparison of Door Access Control Readers: We have come a long way since the early magnetic stripe cards. The new door readers can read RFID card credentials, mobile phone credentials, and biometric credentials. Some of the door readers are combinations of a reader and a controller. This means that all the intelligence is built into the reader at the door. This reader-controller connects to the network. Read more…
How IP Cameras, Access Control, and Intercoms Enhance Security
How the Integration of IP Cameras, Intercoms, and Access Control Increases Safety: What is the best way to use access control, IP camera systems, and intercoms to create lines of defense against intrusions. Surveillance cameras provided by IP camera systems have helped catch the criminals, but what can we do to prevent the intrusions. This article describes the proactive measures we can take to make life safer. Read more…
The Magnetic Door Lock
How to install Mag locks: The magnetic door lock is a unique lock requiring special handling to ensure safety. Since the mag lock holds the door shut and prevents both egress and ingress, additional devices must be present to allow people to exit.
IP Door Access Systems Wiring
The article reviews the wiring topography of various door access systems. We compared the different access control systems and the benefits and disadvantages of each system configuration.
Door Access Control – Frequently Asked Questions FAQs
How does door access control work, what is the most secure access control system, and why do I need door access control management software are some of the questions and answers provided.

Door Access Control and Visitor Management Integration
The combination of access control, temperature scanning, contact tracing, and access to control databases has increased security and health. This article reviews the new technology advances in visitor management and the integration of door access control and other technologies.
Thermal Body Temperature Screening Cameras
How the addition of temperature scanning increase health safety: This article reviews the various technologies used to measure a person’s body temperature, and how they can help monitor people as they enter a secure area.
How Door Access Control Works
The RFID door readers use credentials that have embedded circuits and an antenna. The reader broadcasts a signal that is received by the credential antenna. The broadcasted electrical signal contains enough power to energize the circuit in the credential. This article describes how the technology works.
What is the Best IP Door Access System for You?
Comparison of Door Access Control Systems: We compared three access control systems, the Isonas reader/controller system, the Hartmann control system with a separate IP controller located at the door, and the Biometric IP readers.
How to Increase Security in Apartment Buildings
Network-attached security devices can provide walls of defense that increase safety in apartment buildings. Door access control is one of the first lines of defense.
Biometric Door Access Control
Biometrics provides one of the most secure ways of granting access. It authenticates the person rather than the card that they carry. Biometric identification includes fingerprint, handprint, and facial recognition. The latest technology includes both facial recognition plus body motion and shape. It is one of the more reliable biometric solutions available.
Review of the Biometric Authentication
This document reviews a number of different biometric systems. It compares fingerprint authentication and facial recognition.
The Evolution of Access Control
Remember when access control was limited to fitting a key into a lock and turning? Door control systems have come a long way, and now are easier to install and much more reliable.
Advanced Door Access Control

Wouldn’t it be nice to be able to push a button to initiate campus-wide lockdown? What about integrating IP door access with your IP surveillance system, or controlling what floor a person can go to in the elevator? Or, maybe you would like to use the access system as a visitor management system? Well, the latest network-attached access control systems provide these advanced features as well as many others that can make it easier to control security.
How to Integrate Access Control and Fire Alarm Systems
When the fire alarm goes off, it’s important to make sure that the doors are all unlocked. This article describes how access control and fire alarm systems can be integrated. It also describes how to assure people can escape when the building doesn’t have a fire alarm system.
How Long Range Access Control Readers Work
Long-range access control systems are primarily used to open a gate as you go into a parking area. This article describes how the long-range readers work.
Elevator Control Using Door Access Readers
Door access readers can be used to determine what floors a person can reach depending on their credential authorization. This article describes how we use access control readers along with a special relay control box and software to increase security in a high-rise building.
Comparison of Multimode Biometric Door Readers
Which door reader is best for your application. Take a look at this buyer’s guide. It provides the pros and cons of each type of reader. It includes a comparison of RFID readers, fingerprint, finger vein, facial recognition, and multimodal readers that read more than one physiological characteristic.
Security Provided by Access Control Systems
What can we do to increase our security? By integrating different security systems we increase our safety. IP door access prevents unauthorized access to our buildings, walk-through metal detectors prevent people from bringing in weapons, and using campus-wide paging systems we keep everyone informed of any emergency. This article describes when and how to use these technologies.
Cloud Versus On-Site Door Access Software
Recently Door Access Control software has become available in the cloud. What exactly does this mean and what is better for you? The article compares on-premise software to a cloud platform and provides pros and cons that can help you decide what is best.
How to Install an IP Door Control System
A review of access control technology and how the IP door access systems can be integrated with IP camera systems.
How Does Facial Recognition Work?
Biometric door access control is a more secure method of controlling access. Facial recognition uses a number of algorithms to identify a face.
How does Fingerprint Readers Work?
Fingerprint readers detect the features of a person’s fingerprint and create a digital code that is used as a unique digital template.
Door Access Control Review
This article compares the older door access technology that uses control panels and the latest IP door access intelligent readers. The article compares the total cost of implementation.
How Network Attached IP Paging and Intercoms can Increase Safety
How Intercoms and IP paging systems can improve your safety. Everything you wanted to know about how to add an intercom that can control a door from a remote location.
How to Integrate Door Control With Other IP Systems
Door access control systems have become much more sophisticated, and easier to integrate with other security systems. These new IP door readers integrate with IP video systems, and IP intercoms, providing a much more secure environment.
Biometric Door Control Misconceptions
There are many misconceptions about science and technology. One of the misconceptions is that biometric IP door readers store a picture of your fingerprint or face. Instead of storing a picture of our actual fingerprint or face, the biometric readers captures only a small subset of data and then convert these minutiae points to encrypted binary data.
Technology Notes Newsletter
If you would like to receive our technical newsletter, just fill out the form.
Our Technical Notes newsletter is filled with articles about how the technology works and examples of how it is used. It also includes some great technical jokes and cartoons.
Technical Whitepapers
How to Create the Complete Safety and Security System. This whitepaper describes how to make your world safer by integrating IP camera systems, access control, and emergency paging systems.
Blog
Our blog describes how the security technology works, includes educational notes, describes how to do your own calculations, and how to select the right equipment. We also included examples of how security technology is used.
Technical Videos
These videos provide an overview of the technology. Take a look at the videos describing door access control and IP camera systems.
Network-Attached IP Access Control vs. Analog Separately Wired Access Control Systems
When designing or upgrading a physical security system, one of the key architectural decisions is whether to use network-attached access control (also known as IP-based access control) or a separately wired access control system, often utilizing proprietary multiple wire harnesses.
This video describes the pros and cons of these two systems:
Door access control systems are a foundational part of any physical security strategy. Yet many organizations continue to rely on systems designed for a different era, lacking today’s security capabilities, flexibility, and intelligence. If your access control solution feels rigid, outdated, or difficult to manage, it may be time to consider an upgrade.
This video explains why upgrading your door access control system is not just about new hardware; it’s about better security, greater visibility, and greater control.
- IP Door Access Control and IP Cameras
- How to Select Your Access Control System
- How Biometric Readers Work
- How Walk-Through Metal Detectors Work
- Technology Provides Increased Security
- IP Cameras Are Compatible with IP Access Control Readers
- More…
Technical Support
Security systems can be complex because they include many different components that have to work together. Kintronics is a resource for engineering and integration of all your security projects. We can design your complete system so don’t hesitate to contact us for assistance.
After purchasing your system we make sure that it works exactly the way you expect. You can contact us for help with your installation and any technical support you may need.
We provide technical support and warranty support. Contact us at 1-800-431-1658 or 914-944-3425 whenever you need assistance.