How Write-Once Storage is Used to Protect Video Evidence From Your Ip Surveillance System
One of the objectives of a video security system is to help law enforcement prosecute miscreants. It is important that this digital evidence follow the rules for chain of evidence so it will be acceptable by the courts. It must be treated just like fingerprints, confiscated weapons, and other physical objects that need to be authenticated in court. Ensuring the immutability of digital information can be challenging because a knowledgeable person can modify the evidence if it is not secured. How can we assure that the information has not been edited, deleted, or modified in any way? This article reviews some of the methods for protecting the video chain of evidence.
Procedures Required
In all cases, defined methods of handling and storing the video data need to be followed. Once an incident occurs, the organization should follow a procedure that protects the video. The first step is to transfer the video evidence to secure storage that can’t be changed. This can be DVR-R disc or a protected hard drive. Once the video is transferred, it can be provided to law enforcement.
Exporting the Video
Video can be preserved by transferring it to a DVD-R disc. There is one problem with this solution. These days it is hard to find a DVD-R drive. Instead, we can transfer to a USB-drive. Unfortunately, this is not as secure.
If you can find a DVD-R drive, you can transfer the video to the DVD using video management software (VMS) or your Network Video Recorders (NVR). They both have export functions that make it easy to transfer the information to a DVD (or other media). The recording system exports the video to a .avi file that can be played back on any computer. This works well when there is a short segment of video that depicts the crime.
Some video recording systems can export the video in the same database file structured that is used within the recording program. The application for playing back the video is also exported. This allows anyone to view the video and search for the interesting segments. This technique is best for video evidence that is recorded over a long period.
Using Controlled Hard Drive Video Storage

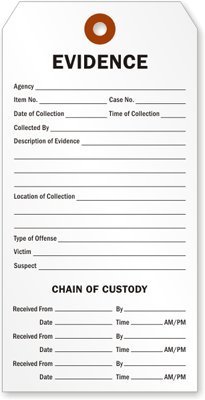
Instead of using a DVD or USB drive, you can use protected hard drive storage. The Criminal Justice Information Services (CJIS) recommends that you should preserve evidence from the time it is collected to the time it is presented in court. To prove the chain of custody, and ultimately show that the evidence has remained intact, prosecutors need service providers who can testify:
- That the evidence offered in court is the same evidence they collected or received.
- To the time and date, the evidence was received or transferred to another provider.
- Assure that there was no tampering with the item while it was in custody.
A challenge in proving chain of custody can arise when the prosecution fails to properly initial and date the evidence or fails to place a case number with it. The storage protected video solution is a good solution for chain of evidence protection. It has security protection build into the hardware-level. It uniquely protects not only the video but also the audit information and audit tools, applications and executables from modification, deletion, sabotage, manipulation and unauthorized access.
HDWrite1X is the product that provides the critical write-protected storage. It can be used with any video recording system. It complies with the CJIS requirements. Video protection is an important addition to your IP camera surveillance system, especially if you are interested in preserving your video for law enforcement.
The Criminal Justice Information Services also requests that any attempt to modify information in the computer be logged. HDWrite1X supports multiple types of real-time intrusion detection. When data tampering is attempted, log entries are generated identifying the attempted intrusion, and the attempt is aborted.
Protecting Your Computer from Malware
Evidence can be destroyed if your computer system is attacked by a virus, ransomware, or other malware. The storage used by your computer system can be protected not only from a person who deliberately tries to change the evidence but also from an external hacking event. The article, “Protecting Your Computer from Malware” describes how to protect your computer system.
If you need help selecting your IP Camera System and the video recording system for your cameras, please contact us at 800-431-1658 in the USA, or 914-944-3425 everywhere else, or use our contact form.