How to Create a One-Button Emergency Response System

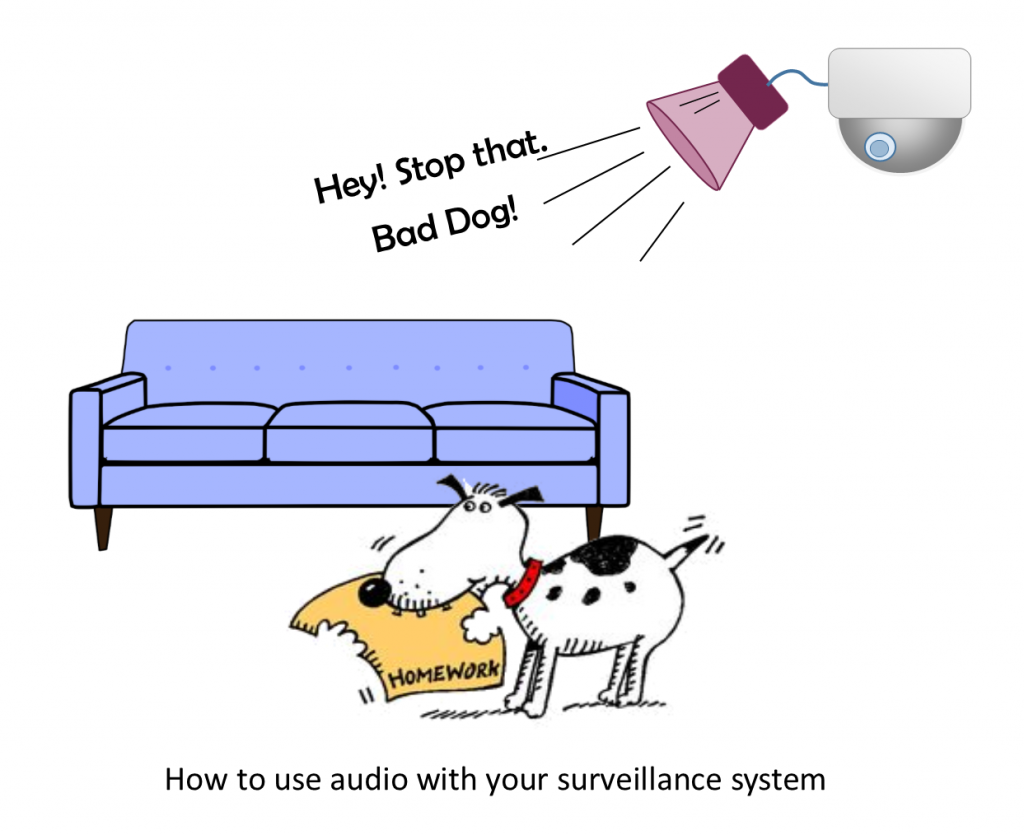
When seconds count, a single-button alert system is essential for your organization’s safety. Whether you need to establish a lockdown or let everyone know about a fire, the rapid notification capability is important.
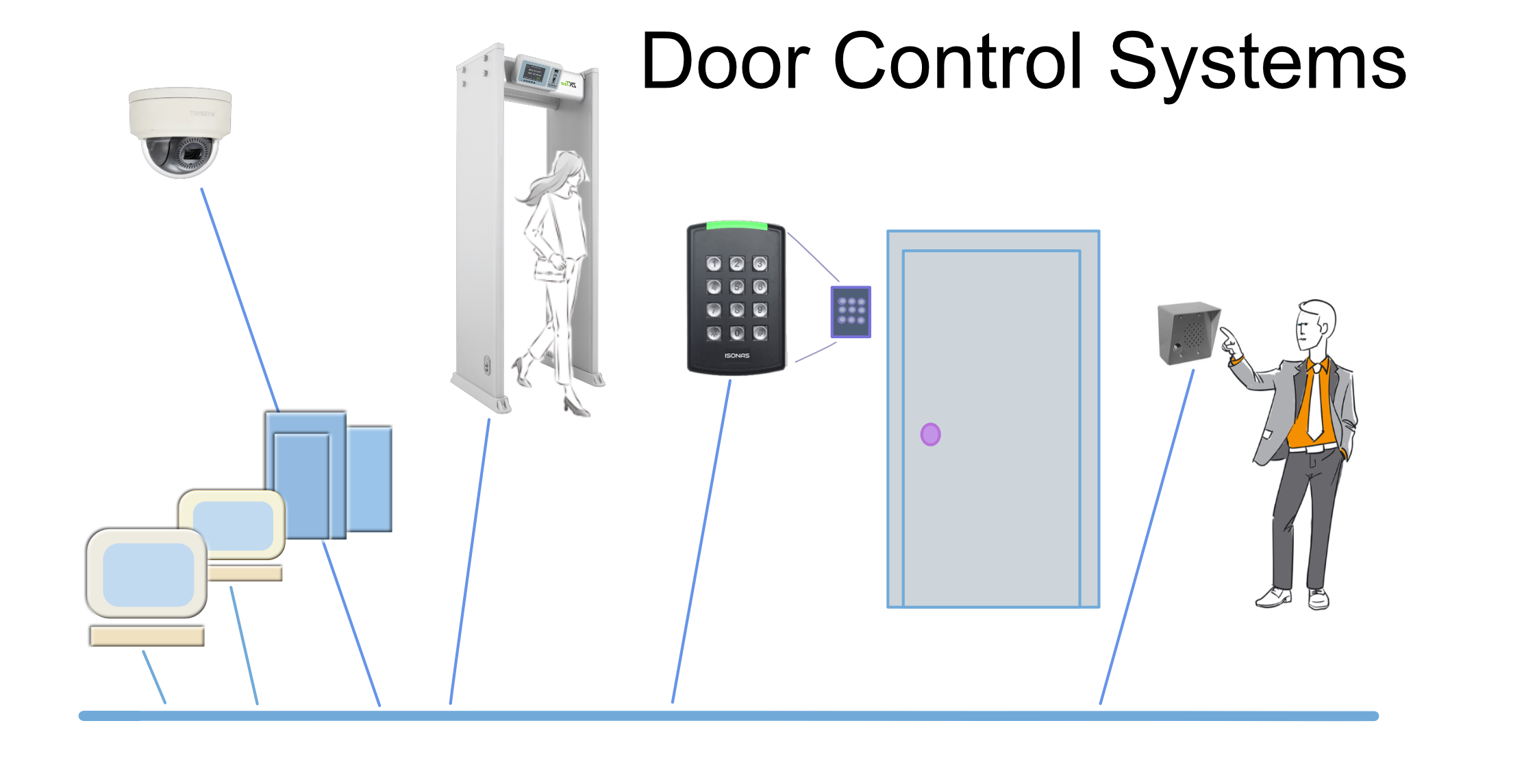
Emergency alert buttons can be placed at various parts of the facility and connected to your IP security system. This means you can provide different responses depending on the location. You can also have unique buttons for specific emergencies. For example, you can respond to a fire or establish a lockdown depending on the button pushed. Here’s how it works: